To avoid crypto scams, one should start with disciplined due diligence and skepticism. Analysts emphasize realistic, well-documented returns, transparent tokenomics, and avoidance of opaque governance or pressure to act quickly. Verification involves cross-checking disclosures, assessing governance access, and evaluating audits. Security relies on standardized wallet setups, layered authentication, and robust backups. Trusted sources must be diverse and verified. The tension between hype and fundamentals remains the key test, a balance that invites further scrutiny and caution.
Spot the Red Flags Before You Invest
Spotting red flags before investing in crypto requires a disciplined, evidence-based approach. The analysis remains cautious and detached, prioritizing verifiable data over hype. Red flags include unrealistic returns, opaque tokenomics, and dubious governance. Scam indicators often surface as pressure to skip due diligence, restricted access to information, and inconsistent auditor reports. Vigilance, skepticism, and transparent disclosures support informed, freedom-oriented decision making.
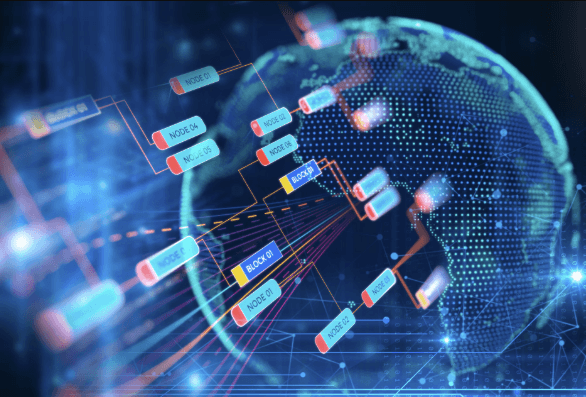
Verify Legitimacy: How to Research Projects and Teams
Verifying legitimacy requires a methodical examination of a project’s core components: the team, the tokenomics in practice, and the governance framework. Analysts compare disclosed information with independent records, seeking transparency and consistency. Key risk indicators emerge from inconsistent timelines, opaque funding use, and elusive governance processes. Tech due diligence assesses code, audits, and founder credibility within robust project governance to reduce exposure.
Protect Your Wallet: Smart Security Defaults
Smart security defaults form the backbone of resilient crypto use, anchoring protection in standardized practices rather than user memory. The analysis emphasizes bold practices and deliberate configurations, reducing human error. Phishing awareness and layered authentication emerge as core components, while security defaults guide repeatable safety. Practitioners advocate careful research of wallet settings, update routines, and backup protocols to sustainably lower scam exposure.
Trusted Sources and Safe Practices for Everyday Crypto
Cautious users monitor hype cycles, corroborate through diverse reputable channels, and avoid impulsive decisions.
Safe routines include upholding privacy, documenting sources, and resisting short-term fads when long-term fundamentals lack clarity.
Frequently Asked Questions
How Do I Recover Funds From a Scam Quickly?
The inquiry regarding recovery focuses on pragmatic actions: first, assess loss scope; second, contact platform support and authorities; third, document evidence; fourth, initiate traceable recovery steps; fifth, preserve security measures; sixth, monitor outcomes; prioritize recovery steps.
Can a Legitimate Project Still Fail Financially?
Yes, a legitimate project can still experience financial failure. Market volatility and regulatory risk impact outcomes; objective analyses show even compliant ventures face setbacks. However, disciplined governance and transparent disclosures mitigate harms, supporting informed decisions for audiences seeking financial freedom.
What Basic Steps Exist if a Suspicious Email Targets Me?
A cautious analyst notes basic steps exist if a suspicious email targets someone: verify sender, avoid links, and report. Phishing remediation steps include checking headers, scanning attachments, and using multi-factor authentication to preserve user autonomy and security.
Are Memecoins Inherently Riskier Than Established Tokens?
Memecoin dynamics often imply higher volatility and liquidity risk, though not inherently unsafe. From a risk assessment perspective, established tokens tend to exhibit stronger fundamentals and longer track records, while memecoins rely on social sentiment and speculative catalysts.
See also: How to Analyze a Crypto Project
How Do I Report Crypto Scams to Authorities?
Reporting channels exist for crypto scams, and authorities urge careful evidence gathering before initiating the scam reporting process; regulators coordinate with regulatory authorities to streamline investigations while preserving user freedoms and safeguarding markets with transparent procedures.
Conclusion
In vigilant ventures, vigilant values verify viability. Thorough timelines, transparent tokenomics, and trustworthy teams temper temptations and thwart theatrical traps. Careful caretaking of crypto conduct cultivates confidence, while cautious curricula cultivate clarity. Comprehensive corroboration, credible audits, and consistent disclosures create compelling, concrete credibility. By benchmarking bias, briefing on boundaries, and balancing risk with reason, users undermine uncertainty. Ultimately, prudent practices prevail: persistent diligence, prudent safeguarding, and perpetual skepticism sustain secure, sound, steadfast crypto journeys.