Analyzing a crypto project requires a disciplined, provenance-minded approach. A reader should start with the whitepaper, checking for verifiable milestones, clear incentives, and disclosed risks. The team, advisors, and backers demand scrutiny of past performance and potential conflicts. Tokenomics must show resilience and long-term value alignment, not hype. Real-world use cases and security postures anchor trust, while governance quality signals durability. The method leaves decisions unsettled, prompting further examination of what truly stands up under scrutiny.
How to Read a Crypto Whitepaper for Real Signals
Evaluating a crypto whitepaper requires more than accepting promises at face value; it demands a disciplined approach that distinguishes signal from hype. The analysis centers on verifiable details, provenance, and risk assessment, not marketing. Clear governance structures and measurable milestones illuminate intent. Community signals, rather than branding, reveal traction, while red flags—ambiguous tokens, opaque security claims, or undefined incentives—prompt prudent caution.
Verifying the Team, Advisors, and Backing
Assessing the credibility of a project requires a careful map of its human and financial inputs: who leads the team, which advisors are attached, and who backs the venture financially.
A rigorous review centers on verifiable team background and demonstrable advisor credibility, cross-checking track records, affiliations, and conflicts of interest. Absence or obfuscation signals risk to freedom-minded stakeholders seeking transparency.
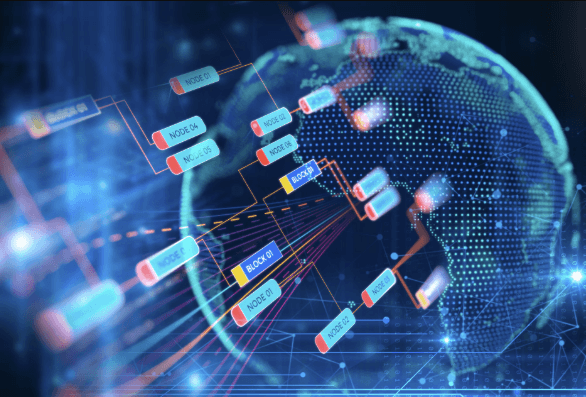
Mapping Tokenomics to Long-Term Value
The analysis remains skeptical yet methodical, tracing provenance and incentives.
It highlights innovative incentives and governance fine tuning as critical leverage points, while cautioning against brittle models, opaque assumptions, and overfitted projections in pursuit of enduring resilience.
Assessing Real-World Use Cases and Security Posture
From the prior focus on aligning tokenomics with enduring value, the analysis now examines how real-world use cases and an organization’s security posture anchor or undermine long-term viability. The assessment remains skeptical and provenance-minded, seeking verifiable evidence of practicality and resilience. It weighs Use cases against regulatory risk, governance, and incident history, framing Security posture as a determinant of durable, freedom-aligned outcomes.
Frequently Asked Questions
How Is Ongoing Governance Actually Executed and Enforced?
Ongoing governance is executed through consensus-driven proposals and encoded voting mechanics, yet enforcement relies on protocol incentives, off-chain accountability, and stakeholder vigilance; governance enforcement remains contingent, skeptical of rhetoric, with provenance-minded actors monitoring for deviations and slippage.
See also: The Future of Token-Based Economies
What Are the Hidden Liquidity Risks in Token Markets?
Hidden liquidity risks in token markets arise from illiquid pools and off-chain incentives, challenging governance enforcement and regulatory compliance; user adoption may spike on hype metrics, but economic resilience and attack preparedness reveal fragility and provenance doubts.
How Does the Project Handle Regulatory Compliance Across Jurisdictions?
Euphemistically observed, the project claims compliance across borders; however, scrutiny shows gaps in governance. It presents compliance mapping and jurisdictional audits as indicators, yet provenance-minded skeptics require independent verification before embracing perceived regulatory alignment.
What Metrics Reveal Actual User Adoption Beyond Hype?
The analysis distinguishes metrics vs hype by examining on-chain activity, retention, and onboarding effectiveness, not just transient price signals. Provenance-minded scrutiny notes active users, transaction depth, and lifecycle engagement, revealing genuine adoption beyond promotional narratives for an audience seeking freedom.
How Resilient Is the Project to Economic Shocks and Attacks?
Resilience testing reveals limited data on economic shock resistance and potential attack surface. The project’s stability hinges on governance, liquidity, and contingencies; skepticism remains warranted as disclosures are sparse, provenance intact, and freedom-minded analyses demand transparent stress scenarios.
Conclusion
The project sits on a ledger of promises and provenance, a lighthouse whose beam wavers with every fog of hype. Like a seed planted in shifting soil, its long-term value hinges on transparent roots: verifiable team, auditable tokenomics, and accountable governance. When signals align—real use, resilient security, and disclosed risks—the beacon steadies. Absent that, the map remains ink on parchment: intriguing, but unproven, its voyage postponed by opacity and brittle assumptions. Skeptical inquiry preserves navigable shores.